Screen Locks Are A Form Of Endpoint Device Security Control
Screen Locks Are A Form Of Endpoint Device Security Control - Automate enforcement of granular device and file policies to stop data leakage and theft. Ad control permissions and removable devices use to streamline endpoint security. Achieve security, compliance and management requirements with endpoint control software.
Ad control permissions and removable devices use to streamline endpoint security. Achieve security, compliance and management requirements with endpoint control software. Automate enforcement of granular device and file policies to stop data leakage and theft.
Achieve security, compliance and management requirements with endpoint control software. Ad control permissions and removable devices use to streamline endpoint security. Automate enforcement of granular device and file policies to stop data leakage and theft.
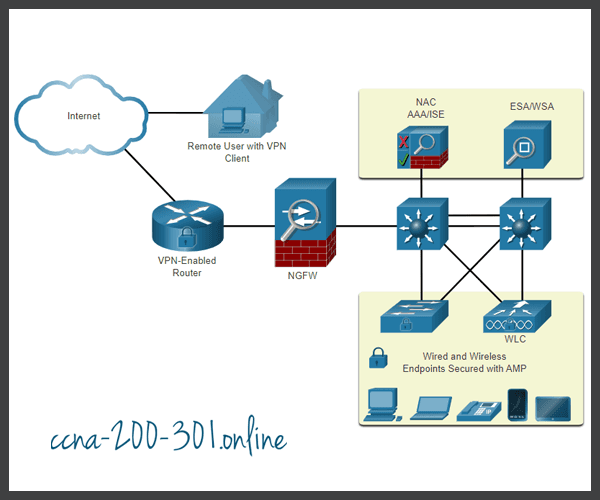
Endpoint Security » CCNA 200301
Achieve security, compliance and management requirements with endpoint control software. Ad control permissions and removable devices use to streamline endpoint security. Automate enforcement of granular device and file policies to stop data leakage and theft.
Endpoint security software Endpoint security management
Ad control permissions and removable devices use to streamline endpoint security. Automate enforcement of granular device and file policies to stop data leakage and theft. Achieve security, compliance and management requirements with endpoint control software.
[Android] Unlock Any Kind Of Screen Locks On Android Without Knowing
Ad control permissions and removable devices use to streamline endpoint security. Achieve security, compliance and management requirements with endpoint control software. Automate enforcement of granular device and file policies to stop data leakage and theft.
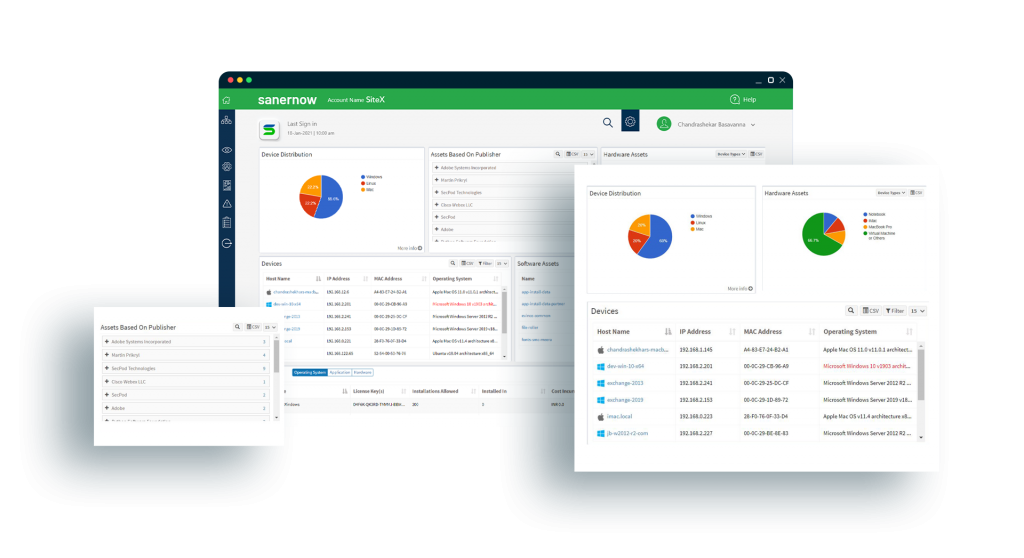
Endpoint Visibility and Control SecPod's SanerNow
Automate enforcement of granular device and file policies to stop data leakage and theft. Achieve security, compliance and management requirements with endpoint control software. Ad control permissions and removable devices use to streamline endpoint security.
Endpoint detection and response is coming in one form or another
Achieve security, compliance and management requirements with endpoint control software. Ad control permissions and removable devices use to streamline endpoint security. Automate enforcement of granular device and file policies to stop data leakage and theft.
Endpoint Protector by CoSoSys Reviews 2023 Details, Pricing
Achieve security, compliance and management requirements with endpoint control software. Ad control permissions and removable devices use to streamline endpoint security. Automate enforcement of granular device and file policies to stop data leakage and theft.
Solved Screen locks are a form of endpoint device security
Achieve security, compliance and management requirements with endpoint control software. Ad control permissions and removable devices use to streamline endpoint security. Automate enforcement of granular device and file policies to stop data leakage and theft.
Screen Locks after 1 minute
Automate enforcement of granular device and file policies to stop data leakage and theft. Ad control permissions and removable devices use to streamline endpoint security. Achieve security, compliance and management requirements with endpoint control software.
Cyber Security Services San Diego Cyber Security Consultant Secure
Achieve security, compliance and management requirements with endpoint control software. Automate enforcement of granular device and file policies to stop data leakage and theft. Ad control permissions and removable devices use to streamline endpoint security.
Understanding What Endpoint Security Is and What it Isn’t 2NDGEAR
Automate enforcement of granular device and file policies to stop data leakage and theft. Achieve security, compliance and management requirements with endpoint control software. Ad control permissions and removable devices use to streamline endpoint security.
Achieve Security, Compliance And Management Requirements With Endpoint Control Software.
Automate enforcement of granular device and file policies to stop data leakage and theft. Ad control permissions and removable devices use to streamline endpoint security.
![[Android] Unlock Any Kind Of Screen Locks On Android Without Knowing](https://techiey.com/wp-content/uploads/2016/11/unlock-1000x665.jpg)